In the labyrinthine corners of the digital underground, platforms with names like StashPatrick evoke a sense of intrigue and notoriety. Discussions surrounding a “StashPatrick CC Shop Login” point to a specific, gated realm within the shadowy world of cybercrime. This article aims not to guide, but to dissect and demystify the mechanics, risks, and stark realities behind such login portals, serving as a critical examination of a dangerous digital ecosystem.
Behind the Login Screen: What “StashPatrick” Allegedly Represents
The name “StashPatrick” itself is a brand within a dark niche. It purportedly functions as an online marketplace, or “carding shop,” where stolen financial data—primarily credit card information (CC)—is bought and sold. The “login” is the digital gatekeeper, separating the curious from the committed, and the public internet from a private, illicit bazaar.
- The Inventory: Behind the login, shops like these allegedly offer “dumps” (data from a card’s magnetic stripe), “CVV2” (card number, expiry, and security code), and sometimes full “fullz” (complete identity packages including name, address, and SSN).
- The Economy: Transactions are almost exclusively conducted in cryptocurrencies like Bitcoin or Monero for anonymity. Vendor ratings, escrow services, and “support” forums mimic legitimate e-commerce to build fraudulent trust.
The Anatomy of a “Shop Login”: Security Through Obscurity
Accessing such a site is not a simple Google search. The process itself is a filter, designed to evade law enforcement and security firms.
- Invitation-Only & Vouched Access: Many of these shops operate on invite-only bases or require existing members to “vouch” for new ones. This creates a closed network, making infiltration difficult.
- The Gateway: Tor & Beyond: The primary login portal for a site like “StashPatrick” would not be a standard “.com” address. It exists on the dark web, accessible only through anonymizing networks like Tor (The Onion Router) using a specific “.onion” URL.
- Security Checks: Even after finding the correct URL, users may face additional hurdles: CAPTCHAs, JavaScript challenges, or requirements to disable certain browser security features—all meant to deter automated bots and scanners.
The Catastrophic Risks: Why Login is a Losing Proposition
For anyone considering seeking out this login, the dangers are immense and multifaceted.
- Legal Peril: Simply attempting to access such a marketplace with intent is a serious crime in most jurisdictions, including conspiracy, computer fraud, and intent to commit fraud. Law enforcement agencies run sophisticated honeypot operations that mimic these shops to trap users at the login stage.
- The Ultimate Scam: Exit Fraud: The cardinal rule of this underworld is there is no honor among thieves. It is exceedingly common for shop administrators to execute an “exit scam”—after building up trust and a large balance in escrow, they shut down the site, stealing all the users’ deposited cryptocurrency. Your first loss could be your initial “funding” deposit.
- Digital Poison: Malware & Tracking: Downloading any required software or scripts from these sites is a high-risk endeavor. Files are often laced with keyloggers, Trojans, or ransomware designed to steal from the thief. Furthermore, adversaries can de-anonymize poorly configured connections.
- Moral & Financial Damage: Beyond legality, participating fuels a global economy that victimizes innocent individuals, causing financial havoc, credit ruin, and significant emotional distress.
The Bigger Picture: The Lifelong of a StashPatrick
Platforms like “StashPatrick” have a predictable, short lifecycle:
- Emergence on dark web forums.
- Growth through marketing and “reliable” vendor reputation.
- Peak activity with high transaction volume.
- Disappearance via exit scam or law enforcement takedown (Operation Darkode, Anom, etc.).
The “login” portal that once stood as a gateway simply vanishes, often with its users’ funds and data.
Conclusion: The Lock That Should Stay Closed
The Stash Patrick CC Shop Login is more than just a username and password field; it is a threshold. Crossing it represents a conscious leap into a high-stakes environment defined by predation, paranoia, and profound legal consequence. It is a system engineered to exploit everyone—the end victims whose cards are stolen, and the would-be criminals who are themselves routinely scammed and tracked.
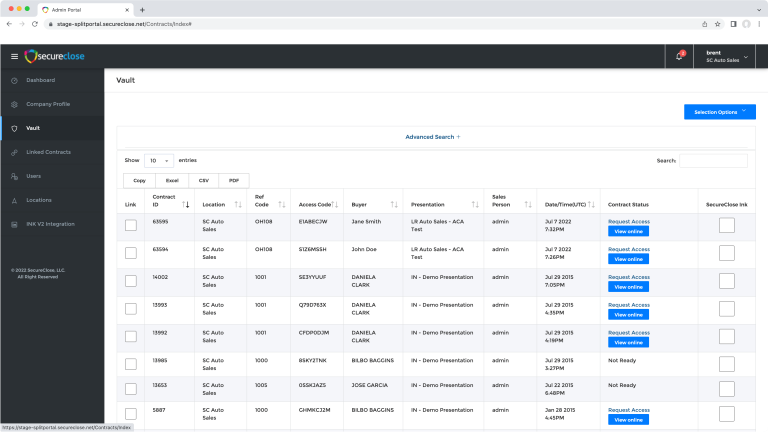
The most secure action one can take is to understand this ecosystem purely from an analytical, avoidant standpoint. Strengthen your own cybersecurity, monitor your financial statements, and recognize that in the digital shadows, the promise of easy gain is always, without exception, a meticulously laid trap. The true “vault” worth seeking is the security of your own digital and financial integrity, protected by strong passwords, vigilance, and lawful conduct.